Today’s post is a recap of some of some of the testing and scenarios I’ve been through. All of this unscientific, not laboratory controlled, and can be interpreted many ways, and here is my take on it all… I’m not saying I understand exactly what I am seeing here, but am open to suggestions.
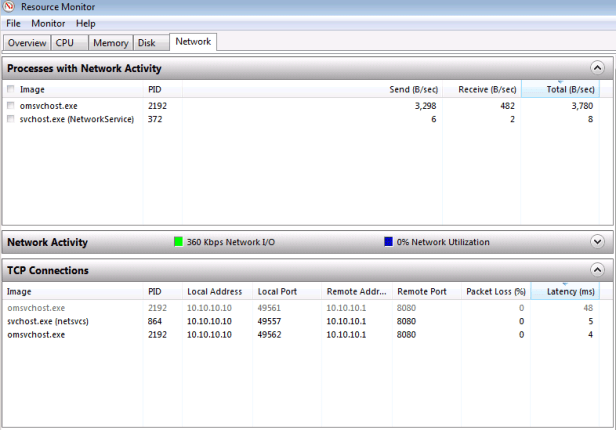
I originally started all of my testing running Windows 7 VMs against a single NIC, proxy/caching only solution, but I noticed that there was alot of traffic that was going outside of the proxy when I was using the Install approach for updating. If I was purely going through Windows Update, the results were as expected, exceptional caching of the Microsoft Update and Windows Update traffic, and incredibly high speed downloads of the updates. The issue that I was seeing was that I hadn’t configured the network to force activity outside of the logged on user to go via a proxy, and I could monitor this easily via Resource Monitor. Here’s a screenshot of what it should look like, note that all the connections are going through 8080, which I have forced via the following steps.
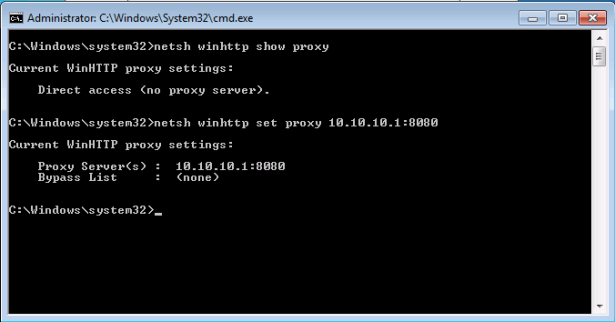
In order to start isolating the network traffic further, I set the TMG VM as the gateway with a private network in Hyper-V, which in my case is 10.10.10.1. If the traffic didn’t go via TMG, it didn’t go anywhere. The IE proxy was set to match TMG, which in my case is 10.10.10.1:8080. All fairly simple and standard for many network configurations. However, because I hadn’t gone through the process of setting up the whole test environment to match a working environment with domain users, domain joined PCs etc, I had to follow another step, which was to run netsh to configure the machine based proxy settings. This was required in order to avoid “The software cannot be installed, 0x80cf402c.” installation error…
Running the netsh command here is quite easy, but first I want to make sure there are no other proxy settings already in place.
Defining a machine based proxy is easy to do.
Kicking off the Intune install succesfully now, and allowing it to update the latest signatures for Intune Endpoint Protection, my client VM NIC shows roughly 140MB of traffic, which matches the incremental traffic on my internally facing NIC on my TMG machine. So far so good. Only about 70MB is showing as moving through my ISP, which also includes traffic from some additional machines on the network, and the TMG TMG NIC is only showing 3MB of traffic.
It’s after this first round of the Intune installation, when I have 42 updates available for download and install, that some of the numbers don’t add up. Check the desktop screenshot below.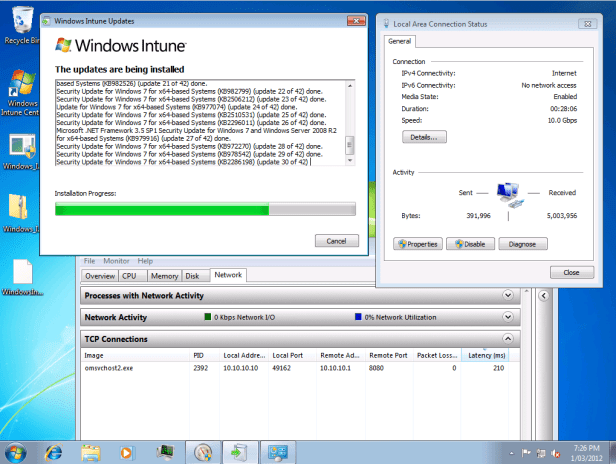
Apparently I received 42 updates, which are now installing, and they were less than 5MB of network traffic. Whether this issue is due to the accuracy of reporting traffic within the VM or some other reason I do not know yet, but would love to hear if you’ve seen the same or received an explanation. The external NIC on the TMG machine is showing less than 1MB of traffic, and the Hyper-V internal NIC is showing around 10MB. Again, at least from the internal NIC perspective, there is a bunch of traffic that just isn’t being reported. It’s not all bad though, this update, and my other network traffic, has generated less than 70MB of traffic. This means that there is definitely caching taking place, it’s the reporting that’s the issue. My TMG cache hit ration has moved up from 67% to 80% over the course of the afternoons testing, so it’s at reporting at least some of this activity.
The takeaways from all of this…
1. Simulating a real environment is going to give you better results when it comes to reproducing them outside of your sandbox
2. Route all traffic via the caching option you go for. There are huge benefits to be had here, both from a bandwidth savings perspective for those of you who pay per MB, and also from the perspective of speed of additional clients downloading the updates. The previous post to this had an image of a download coming down the wire at 111MB/s, which is close to the maximum download speed over Gigabit ethernet. This is what you want.
3. Part of this exercise was reacquainting myself with the Microsoft proxy/firewall family, which I had succesfully avoided for many years. While it had changed quite a bit, for the simple tasks I have it performing it has not been much of a roadblock or learning curve.
4. While I chose to start with a non-SP1 ISO of Windows 7 Ultimate as the base for my VM testing, you are going to save some time using the latest media with SP1 integrated, or manually adding SP1 during your build process.I just wanted the worst possible state for the machines to start with, ensuring that my TMG cache was getting very well used.
5.The numbers don’t lie. The caching works. Big thanks to the Intune team for posting the script on their blog site.