In the second post in this series I introduced one of the first steps in the migration or integration plans, by introducing Azure Active Directory Connect as a way to easily synchronise on-premises identities into Azure Active Directory so that you can start assigning Microsoft 365 Business licences to the users, rather than manually setting up online identities. In this post I’ll introduce some of the synchronisation options you should consider, as well as introducing Hybrid Azure Active join.
For most SMB environments, two of the common settings to enable are Password Hash Sync (PHS) and Seamless Single Sign-On. PHS allows the synchronisaton of a hash of the hash of the Active Directory password, allowing uses to be able to access Microsoft 365 services with the same password they use to access traditional on-premises resources. While there are more advanced options such as Pass Through Authentication (PTA) and Active Directory Federation Services (AD FS), I would only start looking at this options if they address a requirement that AAD Connect can’t. If you need more information on how PHS works, check out Implement password hash synchronization with Azure AD Connect sync.
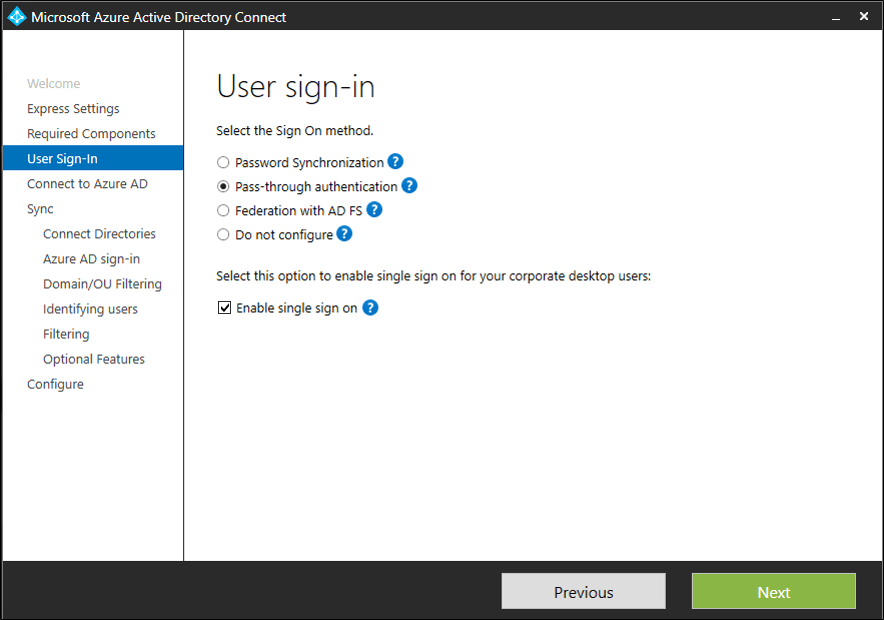
The second recommendation is to enable Seamless Single Sign On, which is configured on User sign in options page of AAD Connect after the sign on method has been selected. This allows for automatic sign in to certain Microsoft 365 related sites, including the Access Panel, Outlook on Web as well as Office 365 portals. Apart from the checkbox option in the image below, you also need to add configure Intranet Zones via Group Policy, full steps can be found here. This will allow the sending of the Kerberos ticket to a cloud endpoint, despite it having an internet address rather than an intranet address.
Once you’ve got this configured, it’s time to start considering what you want to do with Azure AD Hybrid join. If you need to keep Active Directory around for a while and have some GPO dependencies you aren’t ready to move away from, Hybrid AD join allows the automatic registration of AD domain joined devices to AAD, which means they can start being targeted with Conditional Access policies, and you can also enroll them Intune, which means you can start planning and implementing your GPO to MDM migration strategy. This is the topic that I will spend the majority of the next post on, but for now, let’s cover off some non-technical elements of it.
I like to think of Hybrid AADJ as mostly additive, with few real world “gotchya’s”, the bigger issue I see is when it is implemented without it being taken advantage of in order to tick a cloud checkbox. I still encourage you to have pilot users or groups that are pure MDM with AAD ioined, especially when you are looking at leveraging technologies such as Windows Autopilot for longer term management and redeployment, but even just dabbling in some MDM settings to be applied to hybrid AADJ devices is a good start.