In parts 1 and 2 of this blog post series I covered ensuring users and admins are registered for Multi Factor Authentication and enhancements in reporting and then blocking legacy applications, This post will focus on only allowing compliant devices to Conditional Access protected applications. In this post we’ll not only be looking at Conditional Access, but the corresponding requirements in Microsoft Intune.
Let’s start with the Conditional Access options, before stepping across to some of the options we have with device compliance in Intune. Rather than stepping through all of the policy settings that we have covered in the previous posts, we’ll jump straight to configuring the access controls in Grant access.
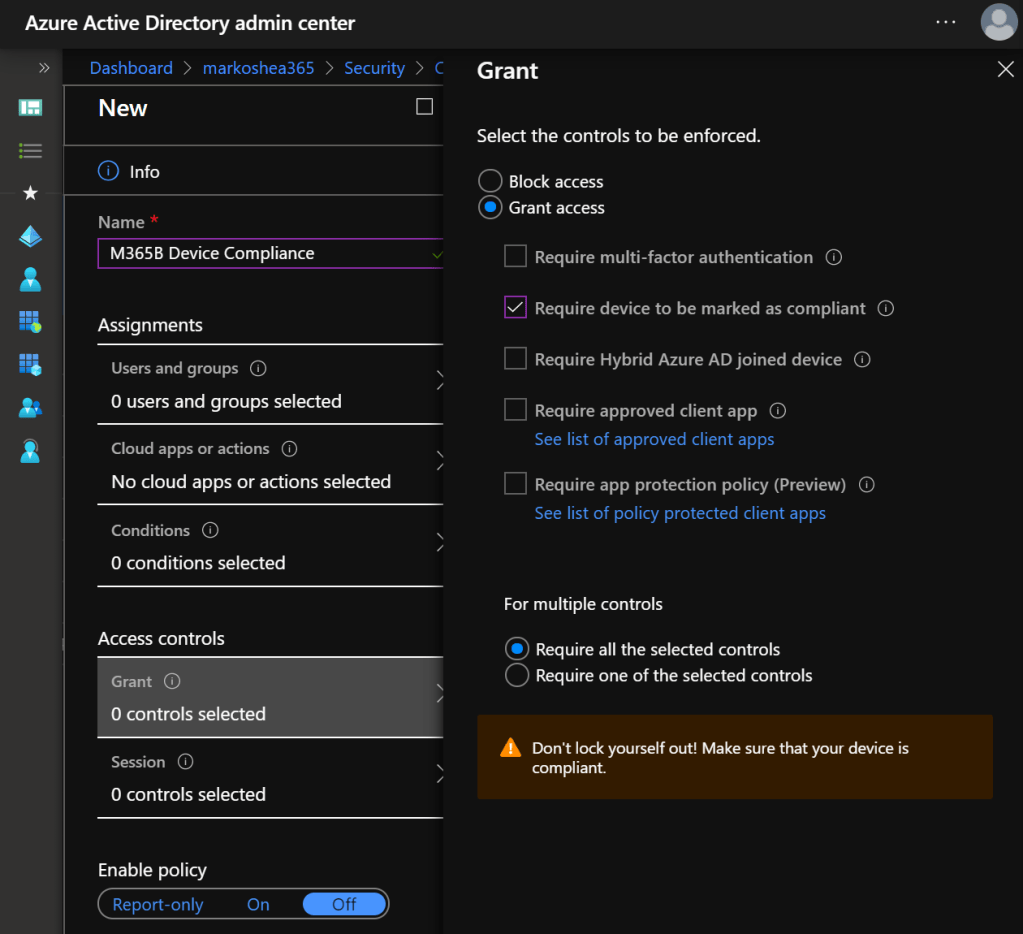
When Require device to be marked as compliant is selected, Intune is relied upon to verify the compliance state of the device, which means we need configuration profiles and compliance policies. It’s recommended to make compliance policies that cover all of the platforms supported by your organization. When creating a policy, you currently have a choice of desktop and mobile platforms as you can see below.
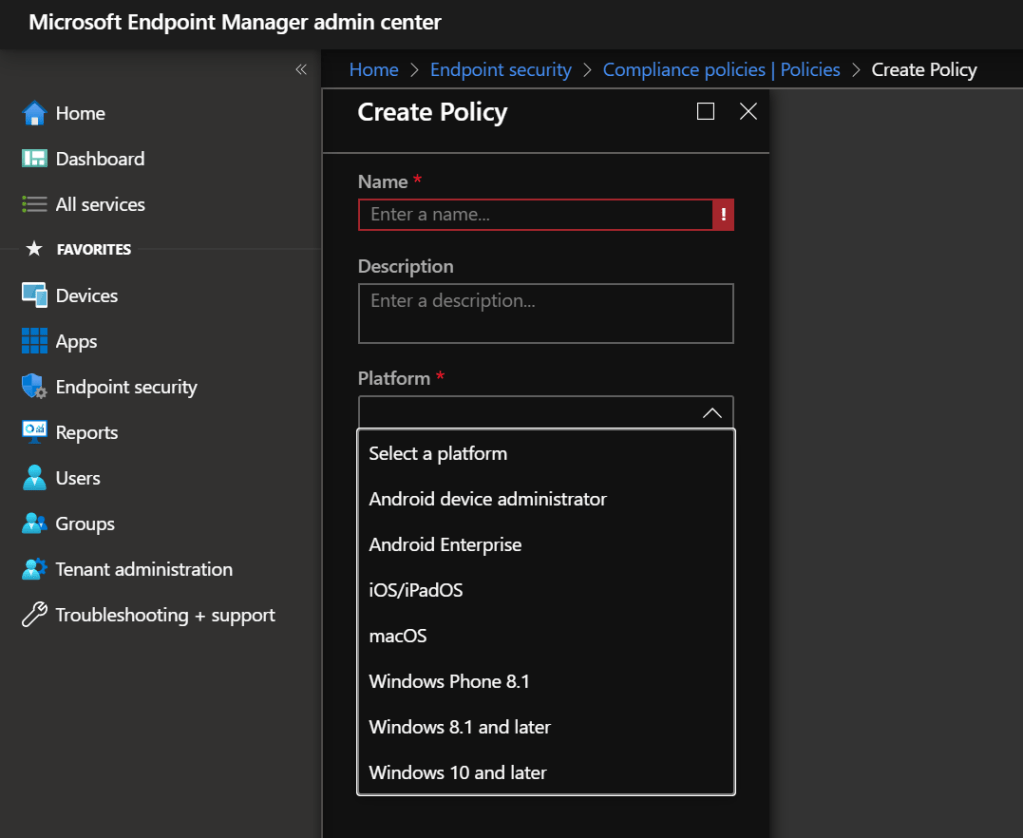
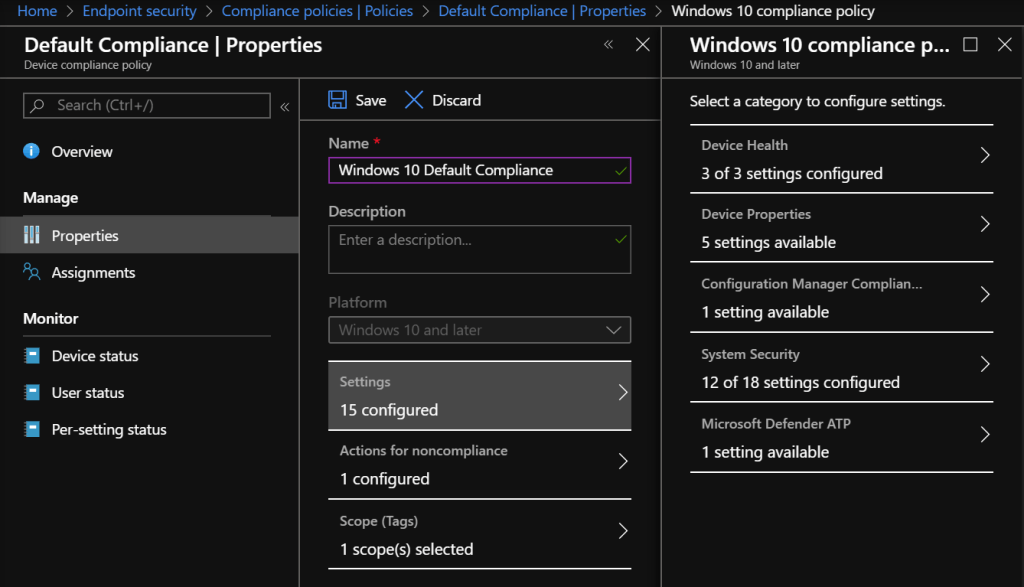
Once we get into the platform options, there are a number of different settings we can verify. I won’t go into all of the options here because there are going to be too many that will be driven by the OS version combined with the hardware capabilities of the devices the organization has. I’ll focus on Windows 10 settings here because we get the option to configure some of these via the Microsoft 365 Business admin center device protection policy settings. The mappings of these options to Intune settings can be found here.
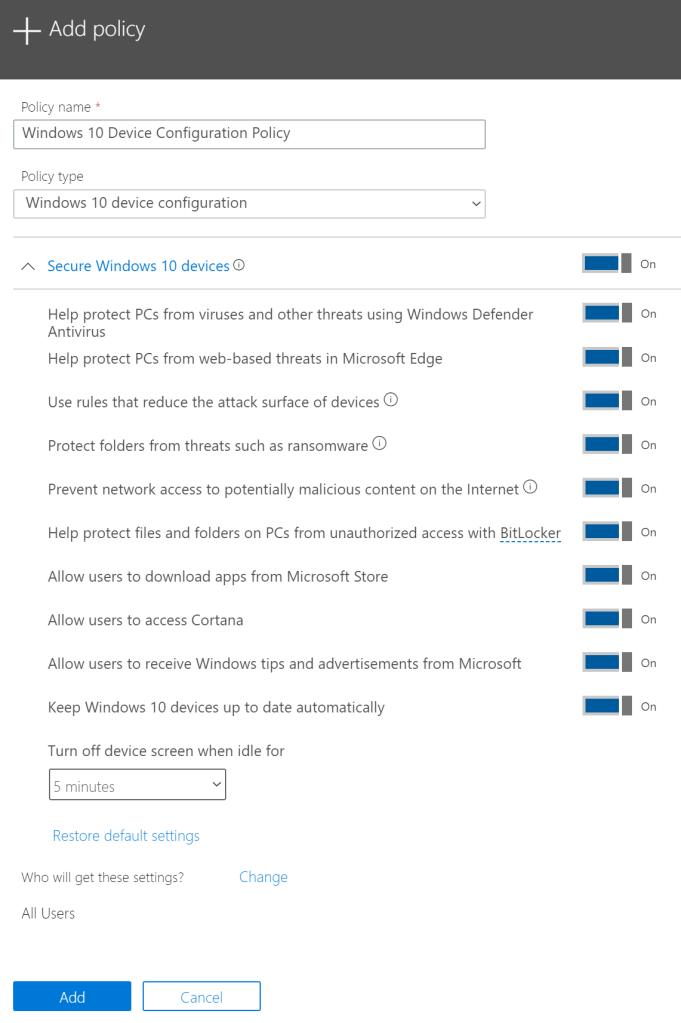
The main recommendation I make here is to leave the policy that you create in Microsoft 365 Business in the state that it’s in, and use it as the starting template for Windows device compliance. If you make changes to this default, they won’t necessarily map back into the Microsoft 365 Business admin center. If you understand that, and even update the description field to reflect this, it’s not as big as an issue, but it’s always nice to have a default to move back to if something doesn’t quite go the way you planned when you start to get more restrictive.
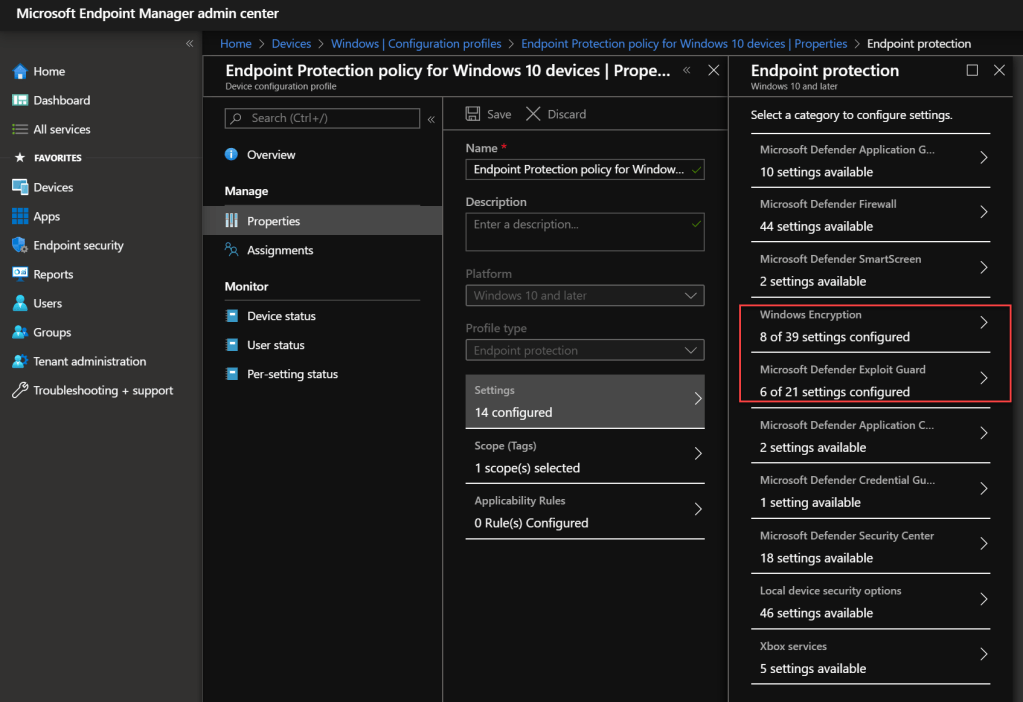
Similarly, you can take the same approach of keeping the Baseline Protection policy for Windows 10 devices that Microsoft 365 Business sets up for you, and then creating additional profiles that either replace or extend the settings it applies and then target them appropriately.
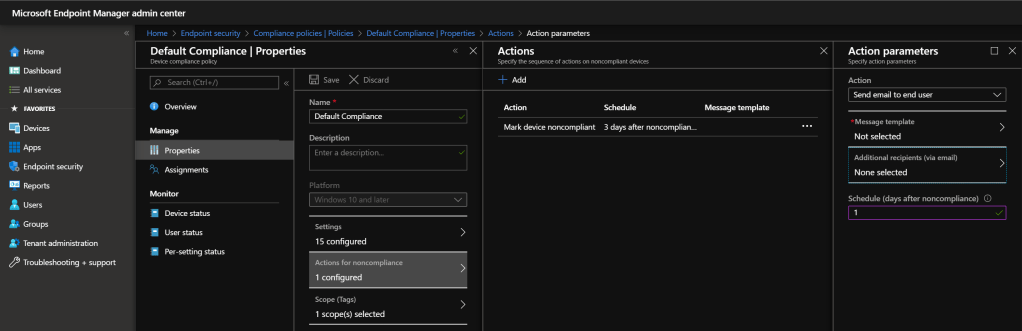
You can choose how many days before a non-compliant device is flagged as non-compliant, giving the device user an opportunity to address the issue or contact support for assistance, and actions include sending an email to the end user, retiring the device, or remotely locking the device.
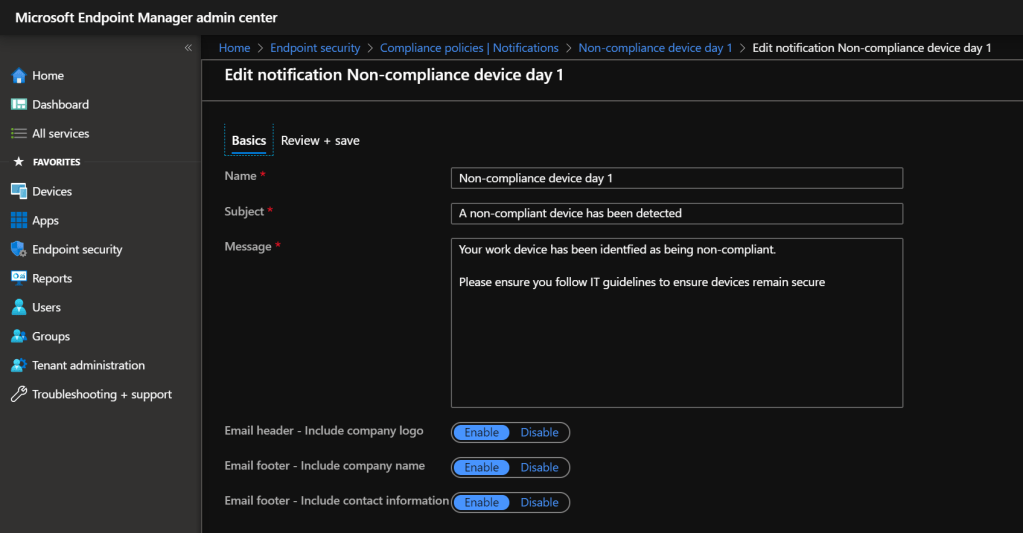
If you choose to start off with email notification you will need to set up a template via Endpoint security – Compliance Policies – Notifications
Hopefully this has given you some ideas of how to leverage Conditional Access capabilities alongside the device configuration options Intune provides with Microsoft 365 Business. Stay tuned for the next post, where we will explore more options for controlling the apps in use on the devices.