One of the new capabilities in Windows 10 that I’m a big fan of is the ability to join Azure Active Directory, here I’ll do a quick walk through of what you see on the Windows 10 client, and what needs to be configured in Azure Active Directory and Intune to allow this to occur.

First up, this screen is presented at the end of a Windows 10 Pro or Windows 10 Enterprise installation if the device has network connectivity. If there is no network connectivity, you will be prompted to create a local account as that will be your only way to sign in. Because these screenshots are from Enterprise, you will also notice that there is no Microsoft Account prompt to be seen. At this point choose the Join Azure AD option and click next.
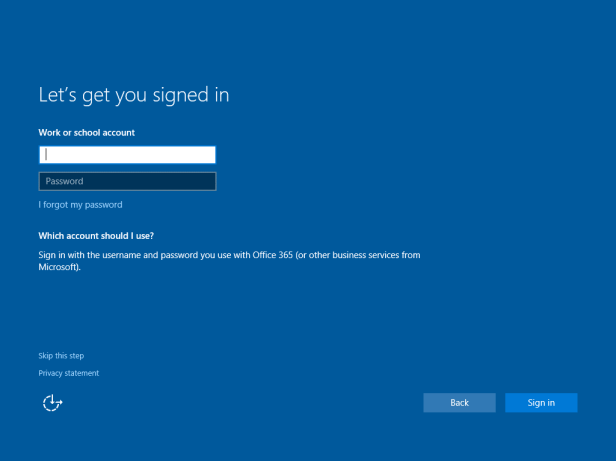
At this screen you can enter the credentials you normally use to access Microsoft Online Services that leverage Azure Active Directory, such as Office 365, CRM Online, Microsoft Intune, Azure Rights Management Service etc
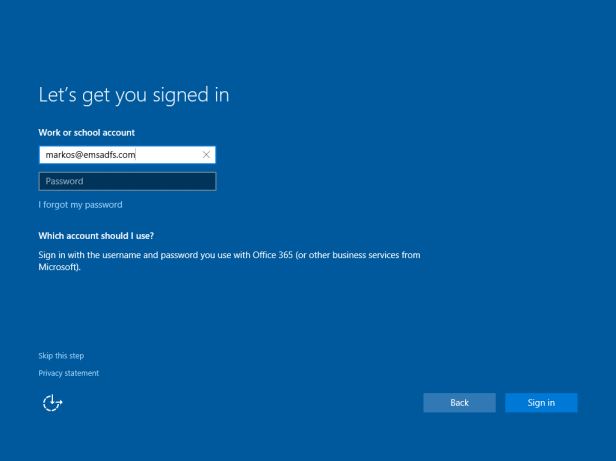
Once you enter your credentials and your password click on Sign In.
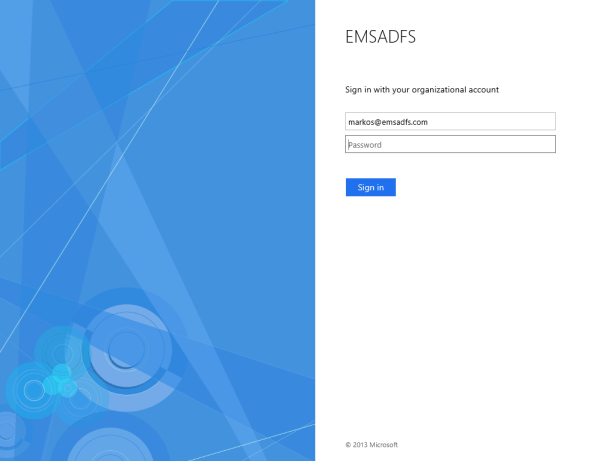
Depending on how, or if, your organisation synchronises your on-premises Active Directory with Azure Active Directory, you may see this log in screen. This screen is presented in this particular environment because AAD Connect is being used for synchronisation, but Active Directory Federation Services is providing the authentication services.

Once the user is authenticated, device enrolment starts taking place. This is normally a fairly quick process.
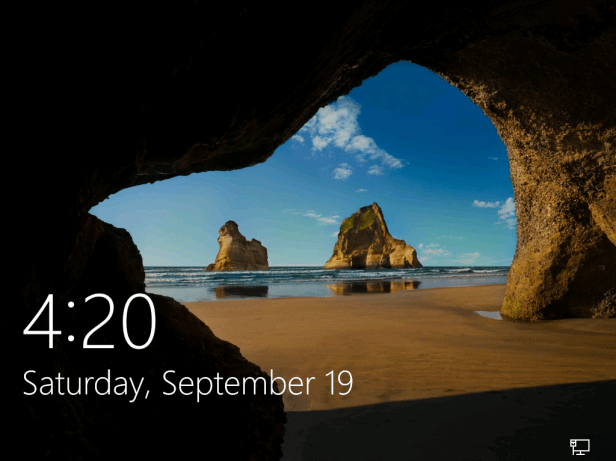
Once device enrolment is complete, you are presented with the default Windows 10 screens.
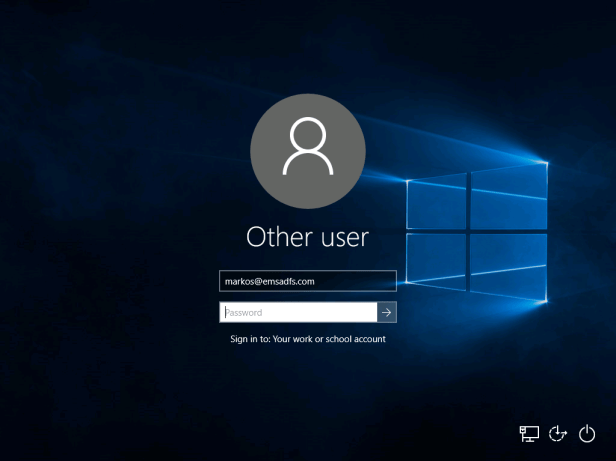
When you get to the login screen, enter the credentials you used to Azure Active Directory Join the device can now be used to log in.

At this point the usual end user first sign in experience kicks off.
Including the setting up your apps screen, which can vary in length based on the performance of the PC, and what else may have been loaded into the image.
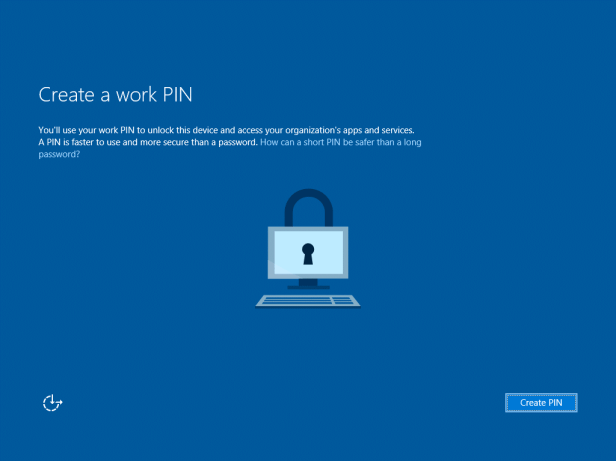
While users don’t have to use a PIN, you can prompt for a PIN, which will become much more important moving forward with the Passport updates that are coming from Microsoft.

Next we are prompted for a multi-factor authentication option.

Clicking Pick a verification method presents a drop down list of the options
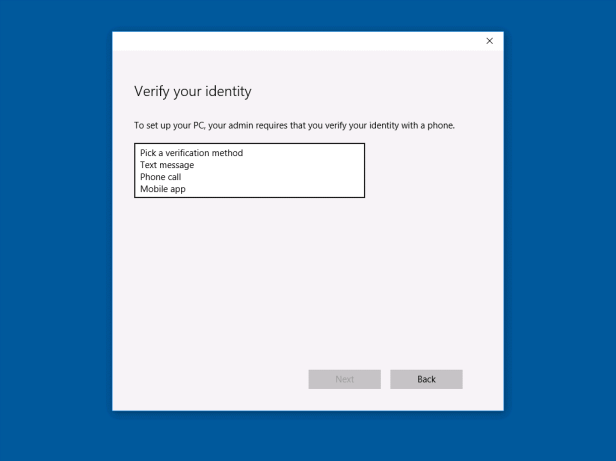
These are text message, phone call and mobile app. Choose the one that makes most sense for you and that will work in most of the environments you will be working from. In my case phone and text aren’t always available, but data always is, so I’ll select Mobile app. Make sure you have installed the Azure Authenticator app on your Windows, iOS or Android device in order to proceed.
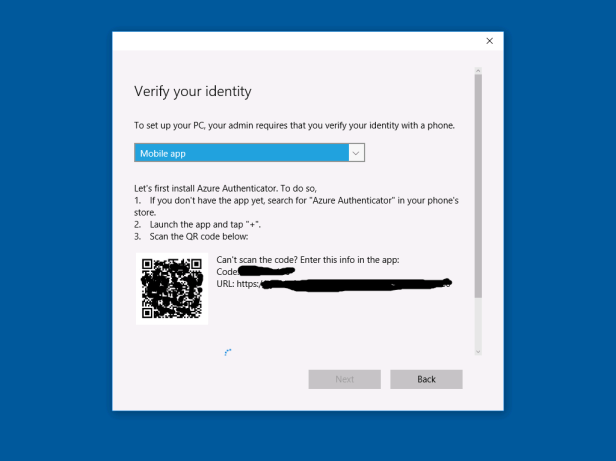
We can then scan the QR code from the app or manually enter the code and the provided URL to authenticate on our mobile device.

Once verification is complete, we see that the app is successfully set up, and we can click on next.
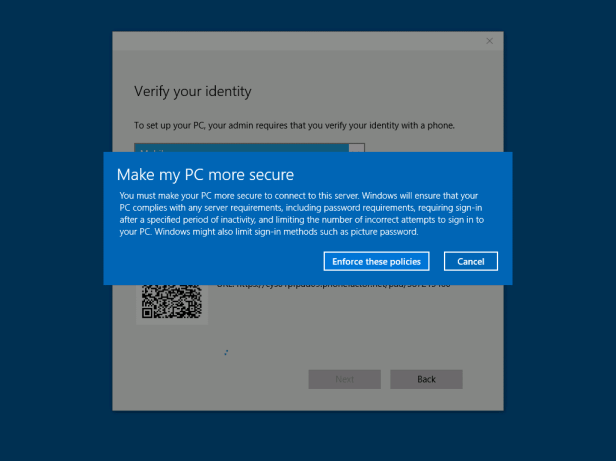
Now we are prompted that corporate policies will be enforced on this device, such as ensuring password policies are met, lock screen requirements and allowable sign in methods, for example.

We are now prompted to receive verification via phone or the Azure Authenticator app we have already setup.

We enter the code we receive and click next.

We can now add phone as a secondary authentication method in case we lose our phone with the configured app.

Now it’s time to create the PIN we were advised about earlier, and you have the ability to customise the requirements depending on the need of your organisation.

In this case a 4 (minimum) digit PIN is required, numbers only, which is what most people would be used to at this point.

Once matching PINS are entered, we land at on the Windows 10 desktop.
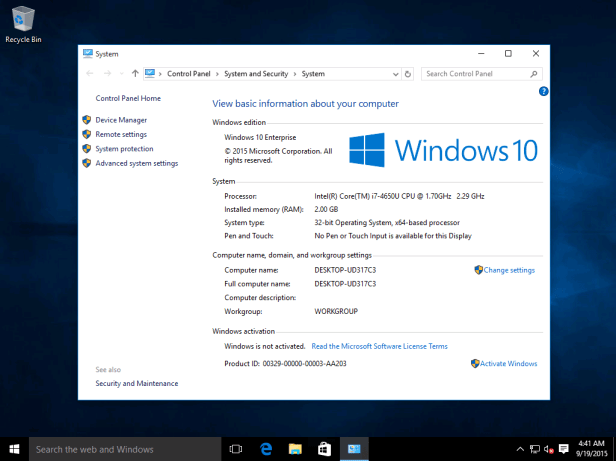
Checking system properties first, note that this machine is not domain joined in the traditional manner, which raises the question how do we check if it has successfully joined Azure Active Directory.
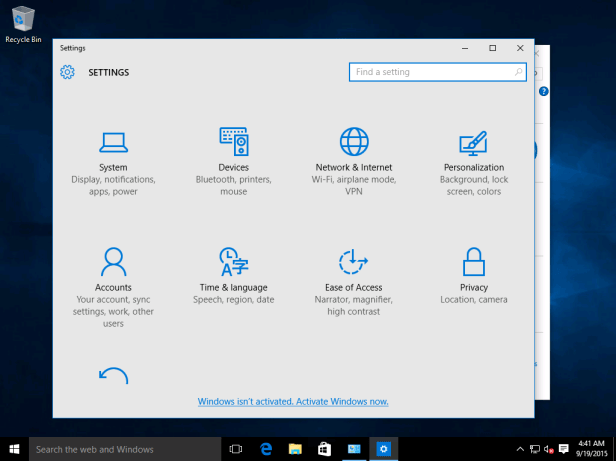
That’s not a difficult task, we go into Settings.

Then select System, About, and here you can see the organization association with emsadfs, the domain that I logged in from.

Earlier it was mentioned that policies would be enforced on the device, and here I will highlight an Intune policy that has been applied by launching Windows Defender.
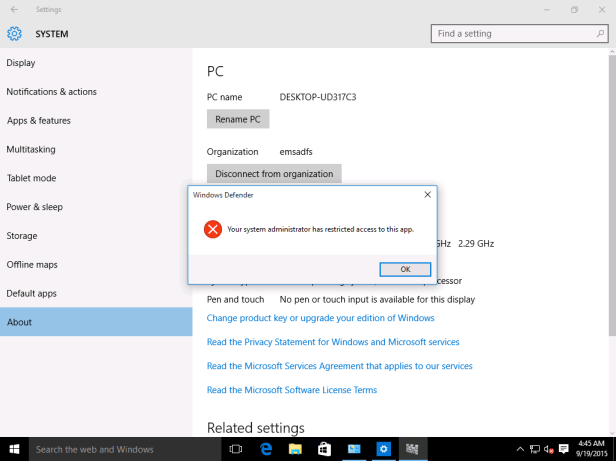
You can see that this action has been restricted, and while it doesn’t give the user any details on the exact mechanism being used, you can see that it at least tells them that it is something that has been set up the system administrator.
In the next post I’ll cover the behind the scenes Azure Active Directory and Intune settings I have enabled to allow the above Azure Active Directory Join scenario to succeed.