In the last post I covered what the end user AAD Join experience could look like, depending on how the underlying cloud services are configured, and in this post I’ll explain some of the configuration settings that are exposed in Azure Active Directory and Intune. Let’s start with the Azure Active Directory configuration settings.

In the Azure Active Directory Configure screen, we have the following options…
Users may join devices to Azure AD – Select the users and groups that are allowed to join devices to Azure AD.
Additional administrators on Azure AD Joined devices – With Azure AD Premium, you can choose which users are granted local administrator rights to the device. Global Administrators and the device owner are granted local administrator rights by default.
Users may register their devices with Azure AD – Allow users to register their devices with Azure AD (Workplace Join). Enrolment with Microsoft Intune or Mobile Device Management for Office 365 requires Device Registration. If you have configured either of these services, ALL will be selected and the button will be disabled.
Require Multi-factor Auth to join devices – Multi-factor authentication is recommended when adding devices to Azure AD. When set to ‘Yes’ users that are adding devices from the internet must first use a second method of authentication.
Maximum number of devices per user – Designates the maximum number of devices a user can have in Azure AD. If a user reaches this quota, they will not be able to add additional devices until one or more of their existing devices are removed.
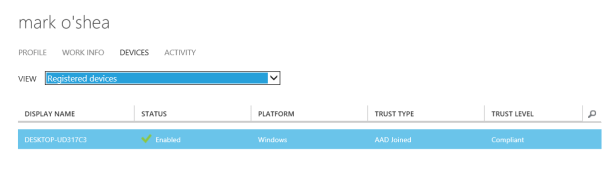
Because I’ve already registered a device for the previous post, I can go to the user’s Devices page to see the devices they have already registered, and we can see that it confirms that it is AAD Joined. But what about non-Windows 10 devces?

Here’s another user with Android and iOS devices, and you can see here that these are Workplace joined, but not AAD Joined.
In order for the next steps to allow auto-enrolment into Intune, you need to make sure that they user has an Intune or Enterprise Mobility Suite license assigned to them.

To configure Intune to allow auto-enrolment as part of the AAD Join process, go to the Applications page for Azure Active Directory.
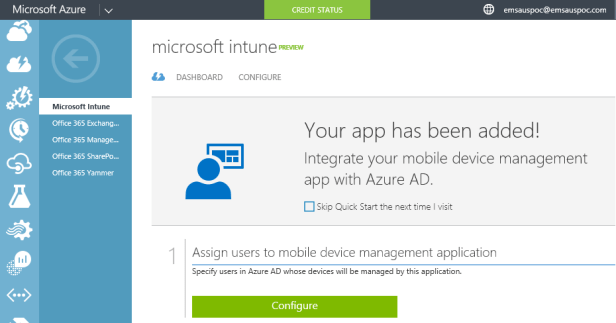
You can check the Skip Quick Start the next time I visit to avoid seeing this screen again, but otherwise just click on Configure.
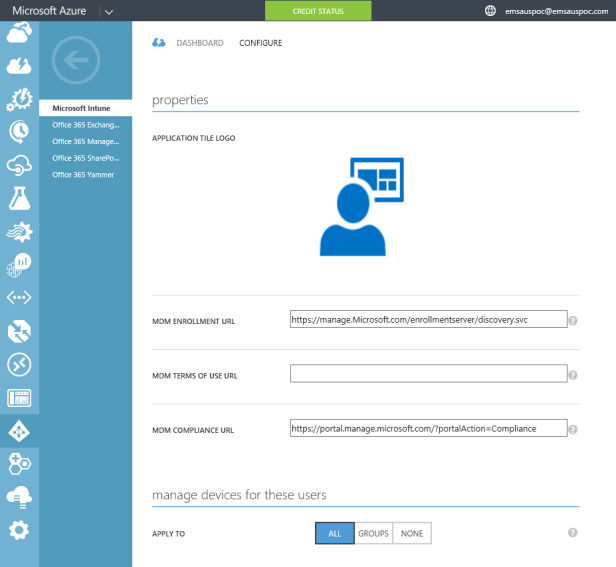
In the Intune properties page we have the following options available…
MDM Enrolment URL – The URL of the enrolment endpoint of the MDM service. The enrolment endpoint is used to enroll devices for management with the MDM service.
MDM Terms of Use URL – The URL of the terms of use endpoint of the MDM service. The terms of use endpoint is used to display the terms of service to end-users before enrolling their devices for management. The terms of use text informs users about the policies that will be enforced on the mobile device.
MDM Compliance URL – The URL of the compliance endpoint of the MDM service. When a user is denied access to a resource from a non-compliant device, a link to the compliance URL is displayed to the user. Users can navigate to this URL hosted by the MDM service, in order to understand why their device is considered non-compliant. Users can also initiate self-service remediation so their device becomes compliant and they can continue to access resources.
Manage devices for these users – Select the groups of users whose devices should be managed by this MDM service.
Let’s switch over to the Intune management portal now to see what is happening over there…

Because of the Auto-enrol enablement being enabled in Azure Active Directory my DESKTOP-UD317C3 Windows 10 device is already showing up as a mobile device inside of the Intune portal.

The final thing is to revisit the Defender restriction I showed in the previous post.
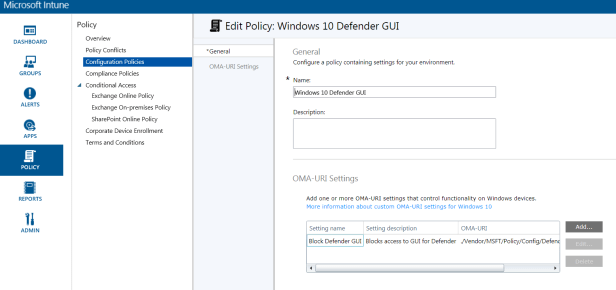
The Defender GUI restriction policy was created with via an OMA-URI setting for Windows 10, which you can find out more about here.