Back in November 2018 I wrote about the Baseline policy: Require MFA for admins that was added to all Azure Active Directory tenants, and mentioned some of the Ignite 2018 announcements regarding upcoming capabilities for end users. These are now in preview, and I’ll go through each of the new additions that have recently appeared in the portal.
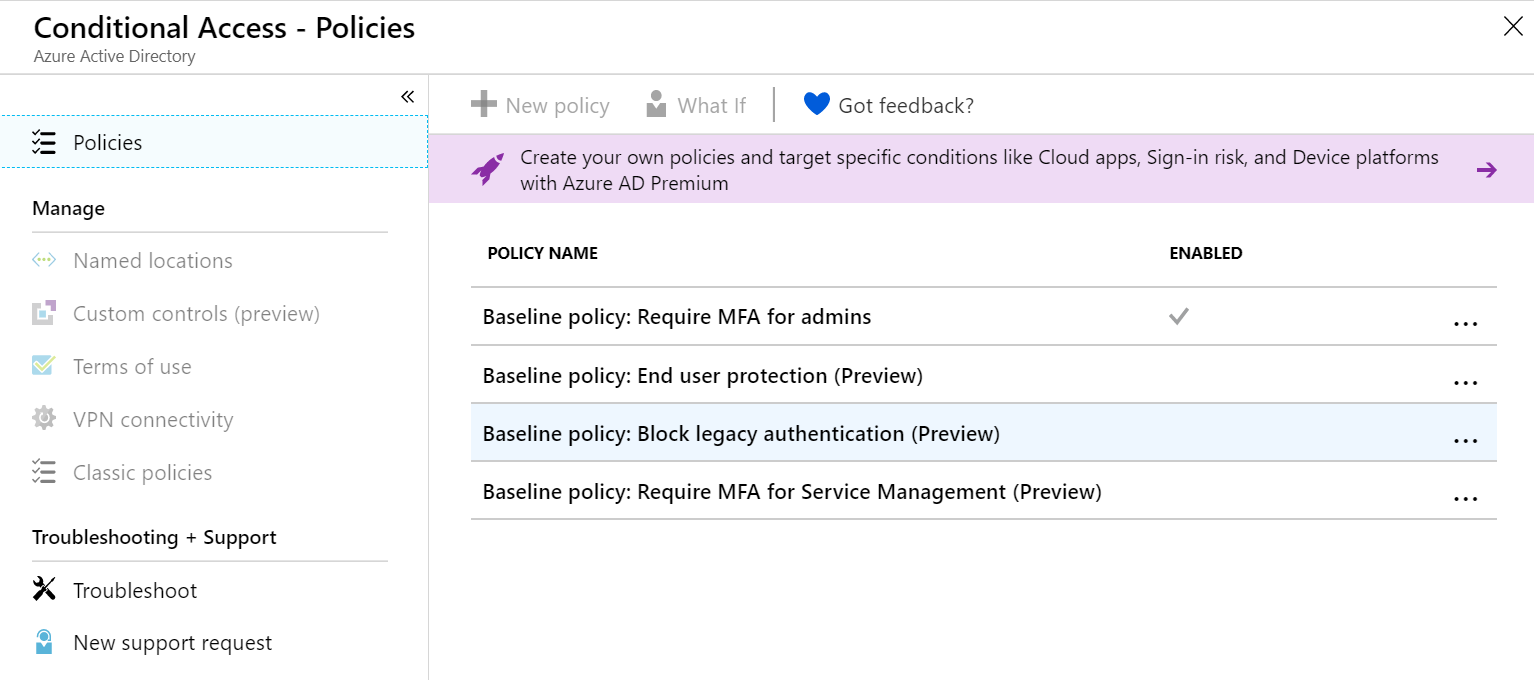
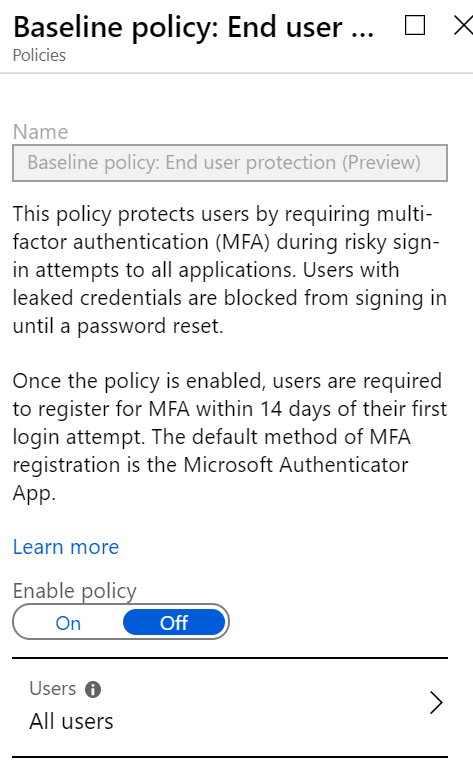
As I’ve covered Baseline policy: Require MFA for Admins previously, I’ll jump straight in to Baseline policy: End user protection (Preview). This policy requires users to complete MFA registration within 14 days of signing in, using the Microsoft Authenticator App for iOS or Android as the default MFA option. Users should only receive MFA prompts if a risky sign-in is detected
If valid user credentials appear on a leaked password list, it is blocked until the user’s password is reset. If the user has a AAD Premium assigned and the capability is enabled in the tenant, they can perform a self service password reset, otherwise the password reset needs to be performed by IT.
This policy applies to all users, so you need to ensure that it isn’t going to cause conflicts with any of the current usage requirements, and will cause problems for apps that rely on legacy protocols. You can exclude users from the policy, so it’s important to ensure that the emergency access accounts, service accounts and service principles are excluded.
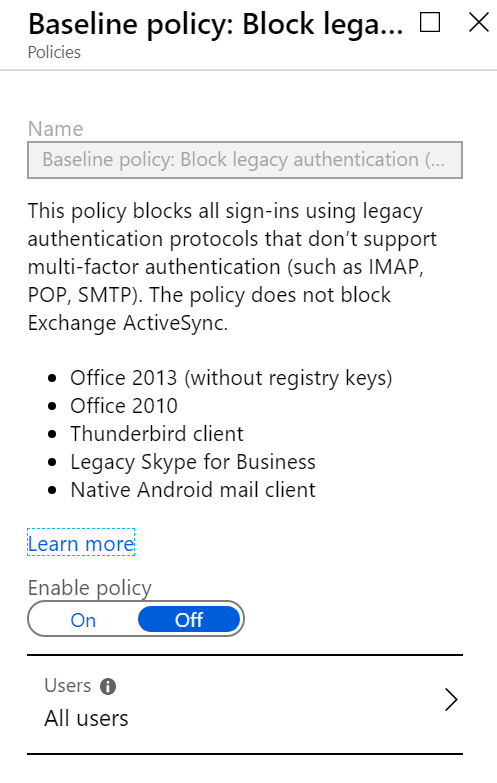
Moving on to Baseline policy: Block legacy authentication (Preview), we are now deliberately targeting protocols that don’t support MFA, including IMAP, POP3 and SMTP. Why these protocols? They are commonly used as a the entry point into services like Office 365, without the ability to leverage MFA.
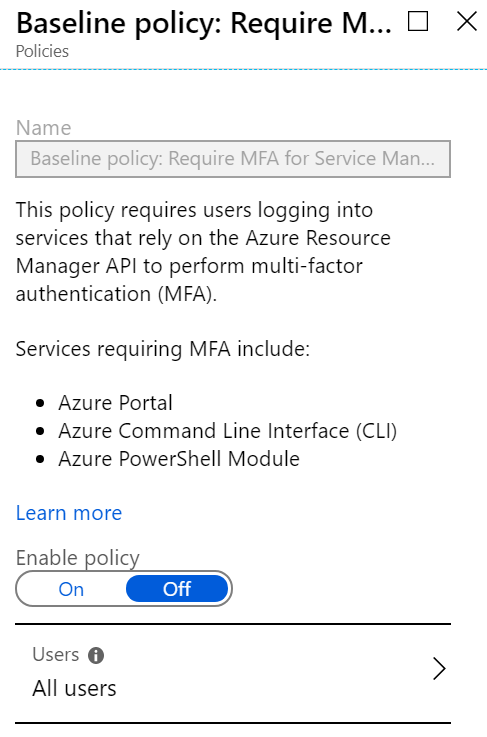
The third new addition is Baseline policy: Require MFA for Service Management (Preview) requires MFA for sign ins for users leveraging the Azure Portal, Azure CLI and Azure PowerShell. Once again, this will apply to all applicable users once applied, so you will need to ensure that you have set up the appropriate exclusions.
This is just a quick overview, as I’ve tried to sneak this post out as I only saw these light up today, but for now, head on over to What are baseline policies?