This is going to be a series of posts on the process of adding Microsoft Defender Advanced Threat Protection (MDATP) into a Microsoft 365 Business Premium (M365BP) tenant, and this first post will start with an alternate approach to how you might normally set up a test environment if you are also ramping up your Azure skills.
I’ll start by saying this isn’t exactly a direct path to achieving integration, but think of it as showing a few of the tips and tricks I use when I’m setting up a new demonstration environment for events or for training purposes. Hopefully there are a few things in today’s post that you weren’t aware of, and that you can potentially work into some production environment defaults as well.
The main reason I’m taking this approach, rather than just signing up for a trial, is that it seems that it’s getting harder to set up a free trial without providing more details including a credit card number, for example, and the only pre-requisite for the approach I’m using is that you can sign in to the Azure portal and can create a new Azure Active Directory (AAD) tenant.
Step 1: Create A New AAD Tenant
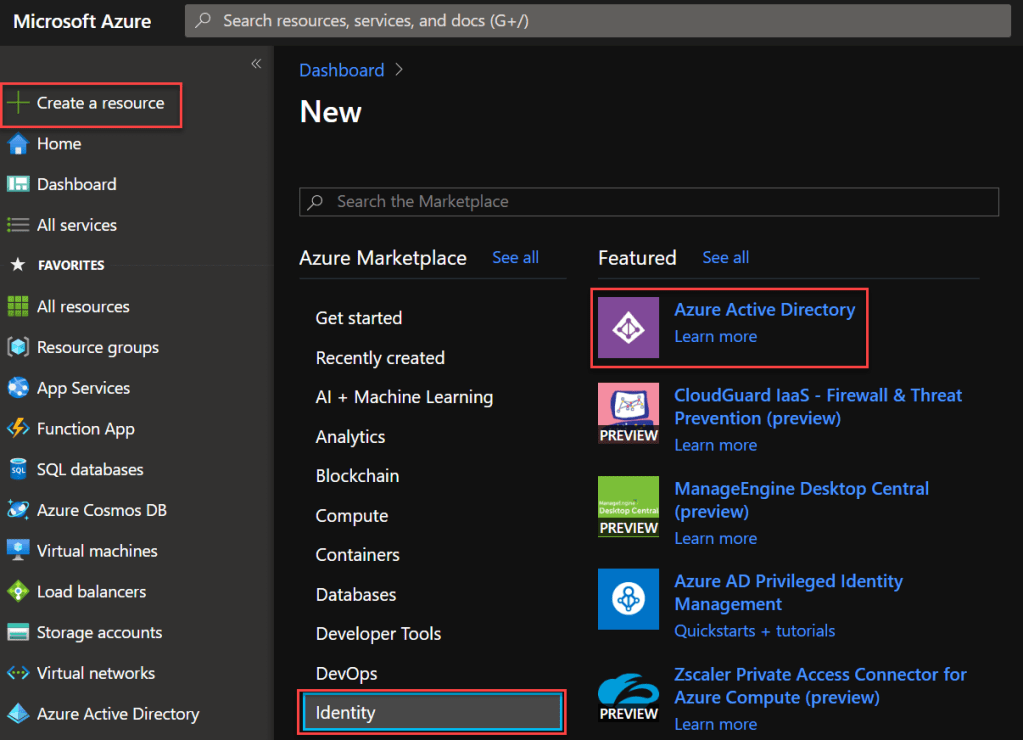
There are a few different ways to create this tenant, but let’s start one that is free from other services as the basis. The easiest way to do this is via the Azure Portal. Select Create a resource, Identity and then Azure Active Directory
Next up create an easy to remember domain name. As this is only a test/demo environment I won’t be verifying a domain name as part of this, even though you would be doing this in a production environment.
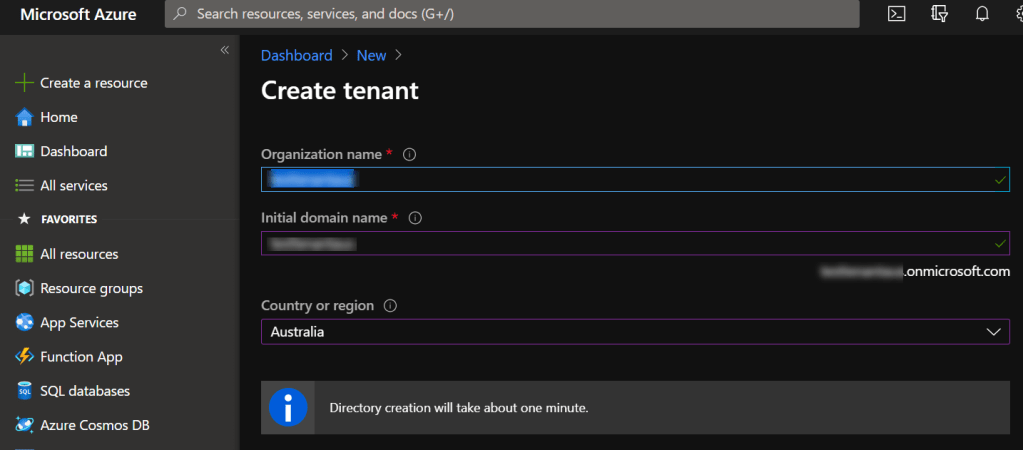
Before long you should see the link to start managing the directory you have just created.
Clicking on here takes you to the your new tenant, where the account used to create it is now showing up as an external AAD user, but with Global Admin privileges.
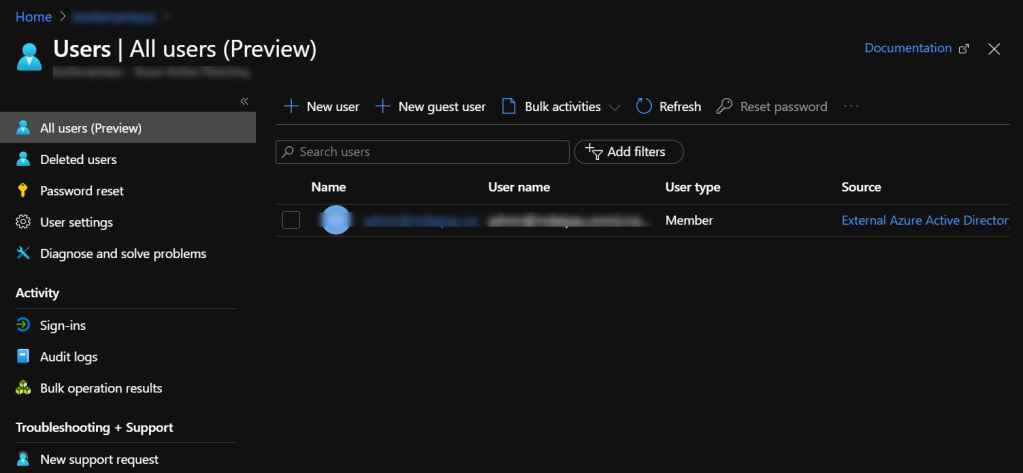
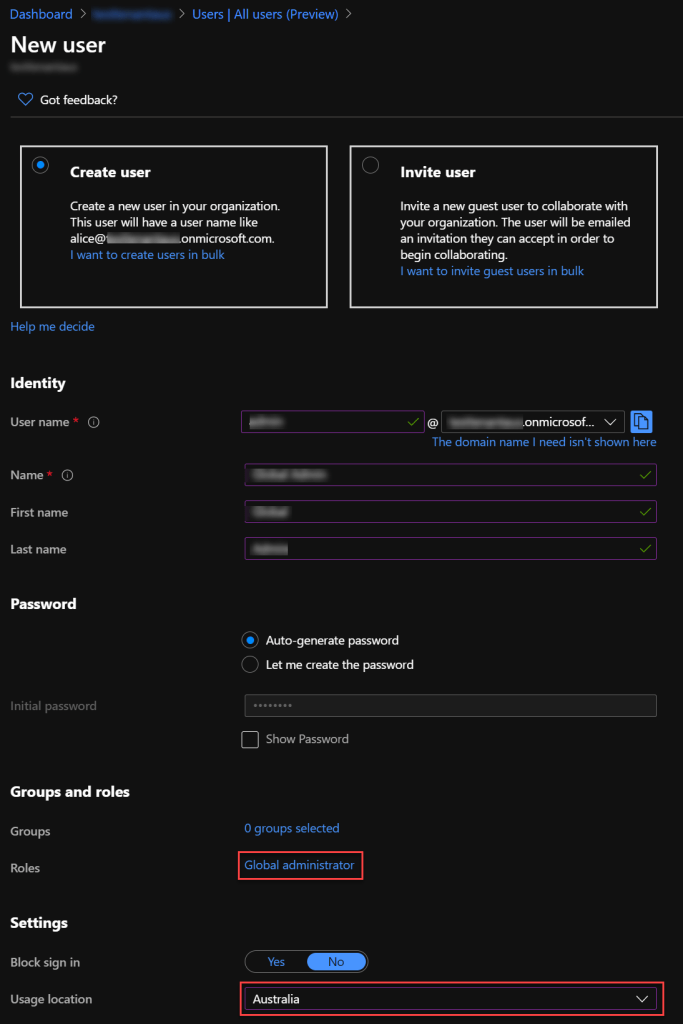
The next step is to click New user, and provide the relevant details. Make sure you add the Global Admin role to the user, as well as setting a usage location.
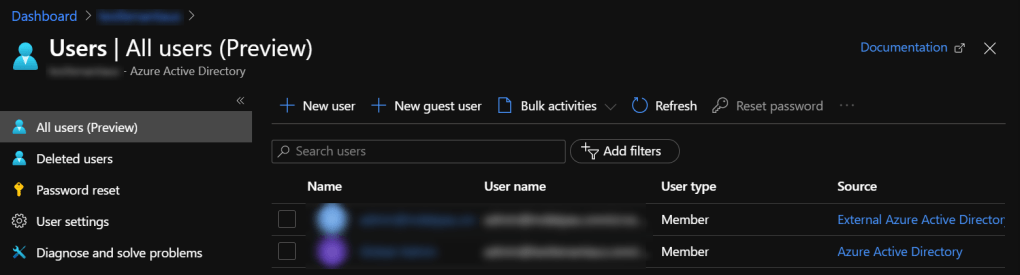
Final step before we switch gears slightly, verifying that we have succesfully created the new account with Azure Active Directory as the source, alongside the we see it alongside the external Azure Active Directory account.
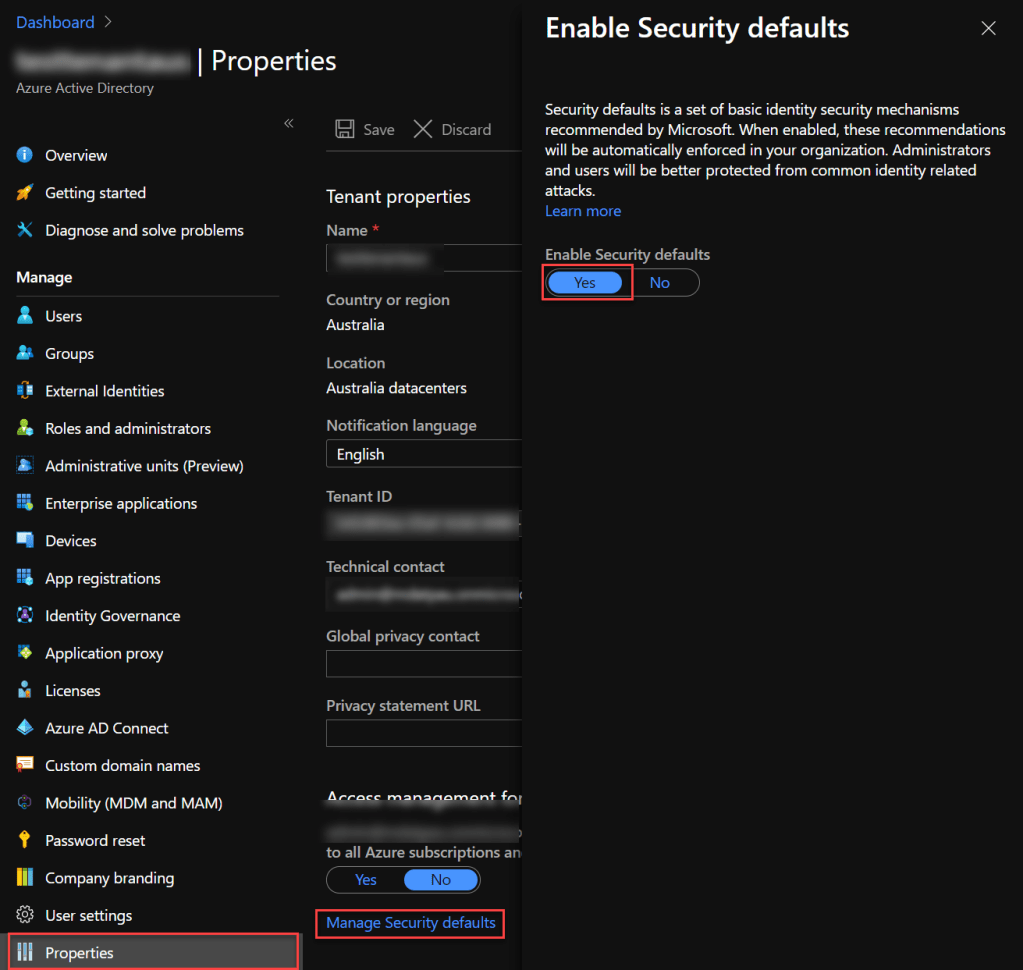
The final thing I recommend doing here is changing a few settings for the new AAD tenant before signing in to it as the new user. First of all, let’s turn on some default security settings. Choose Azure Active Directory Properties, Manage Security defaults, Enable Security defaults.
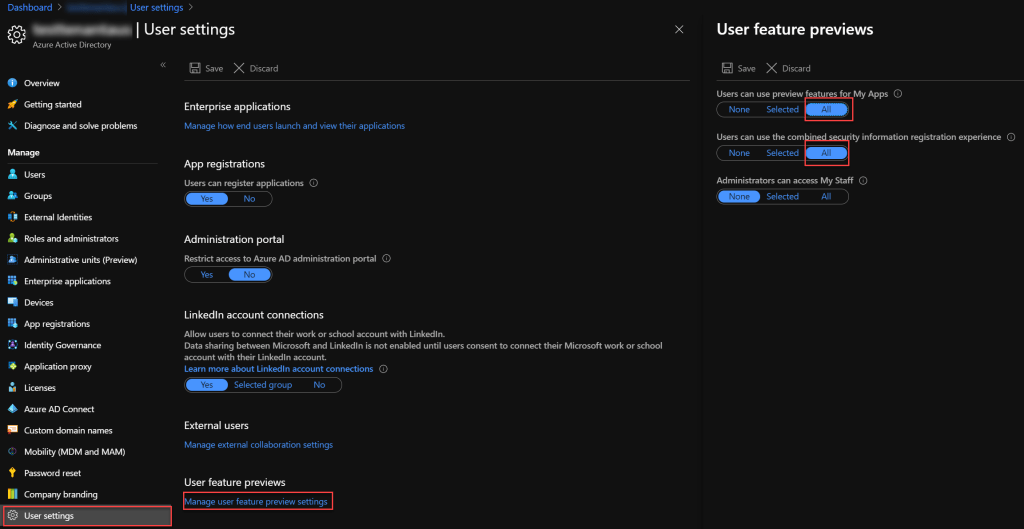
Up next, enable the User feature previews, but the one we are most interested to start with is Users can use the combined security information registration experience, which integrates SSPR with MFA enrolment.
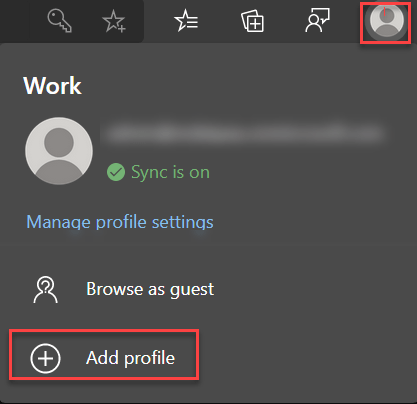
Step 2: Create A New Edge Profile (Optional, but recommended)
Wait, what? Think of this is a convenience step, and also as a reminder to those of you who aren’t taking as much advantage of Edge profiles as you could be.
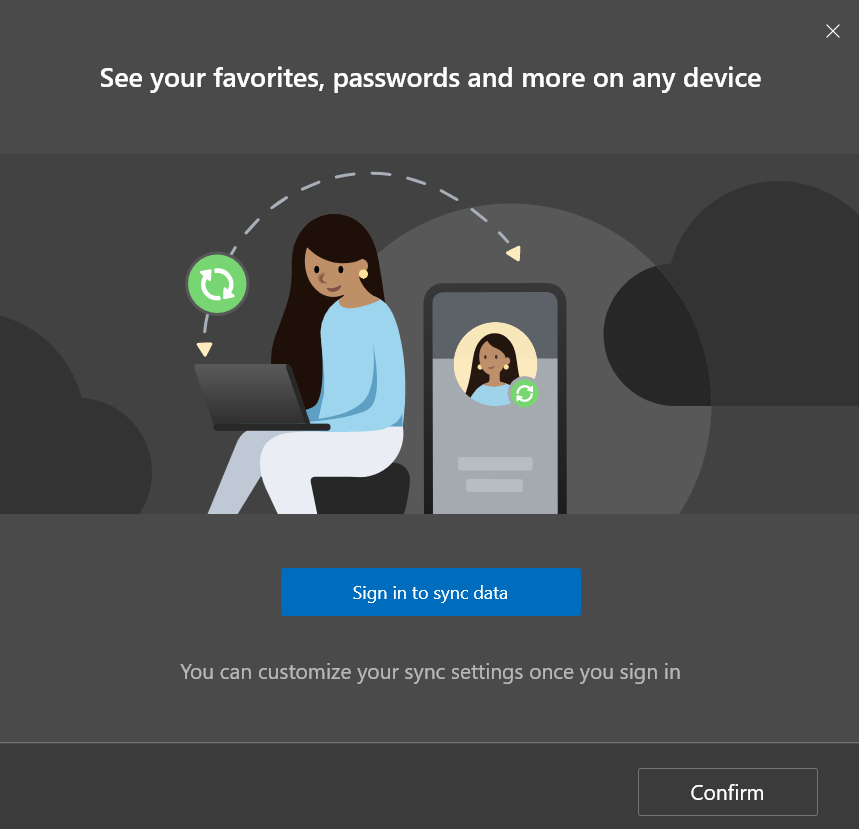
You get the option to Sign in to sync data, and this is one that I always choose as I’m more than likely going to be signing in to this newly created account from a a few different physical and virtual machines..
As this as an AAD account, you need to choose Work or school account
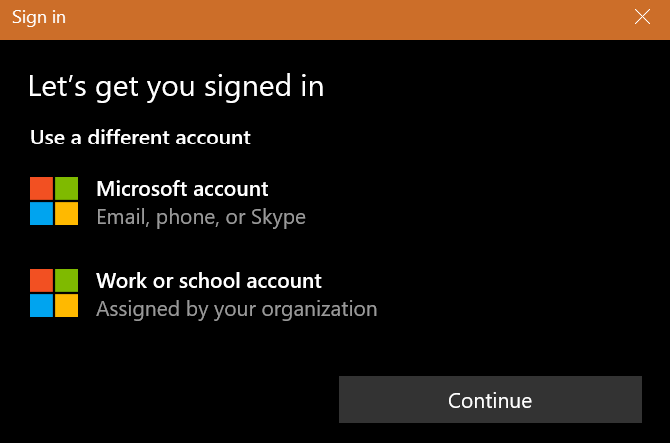
That brings us to the standard Sign in screen where you enter your freshly created account details.
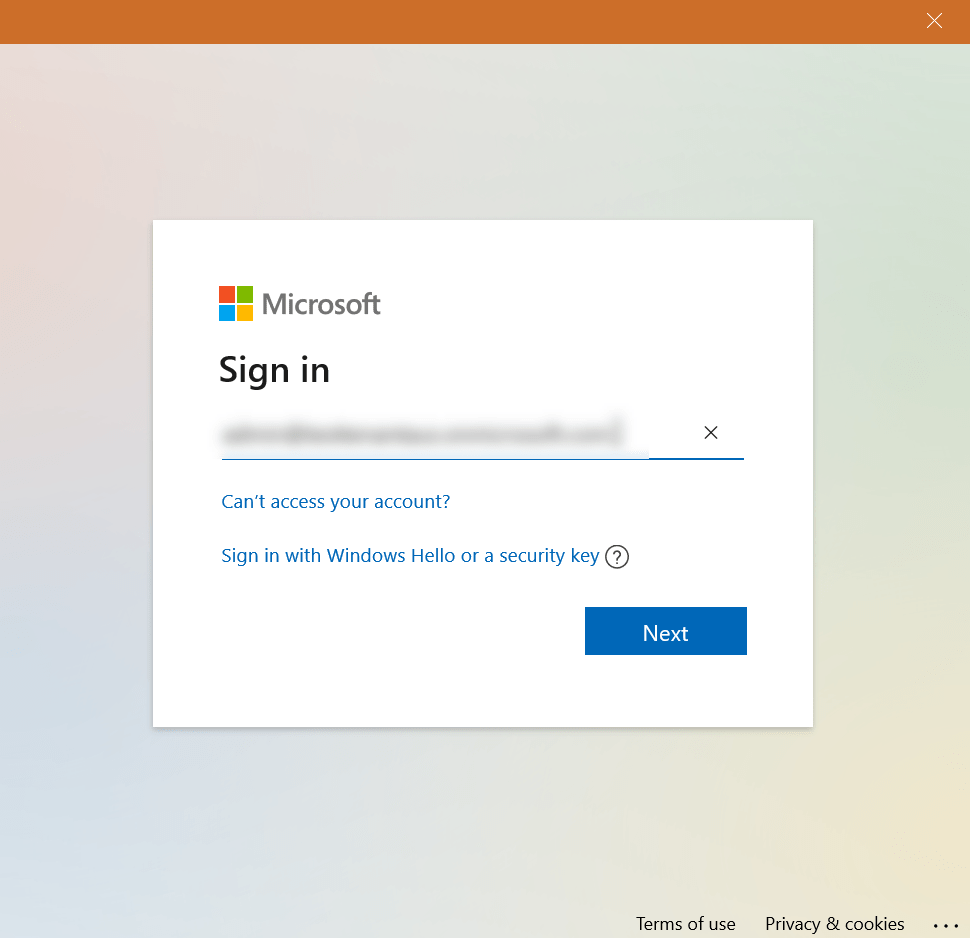
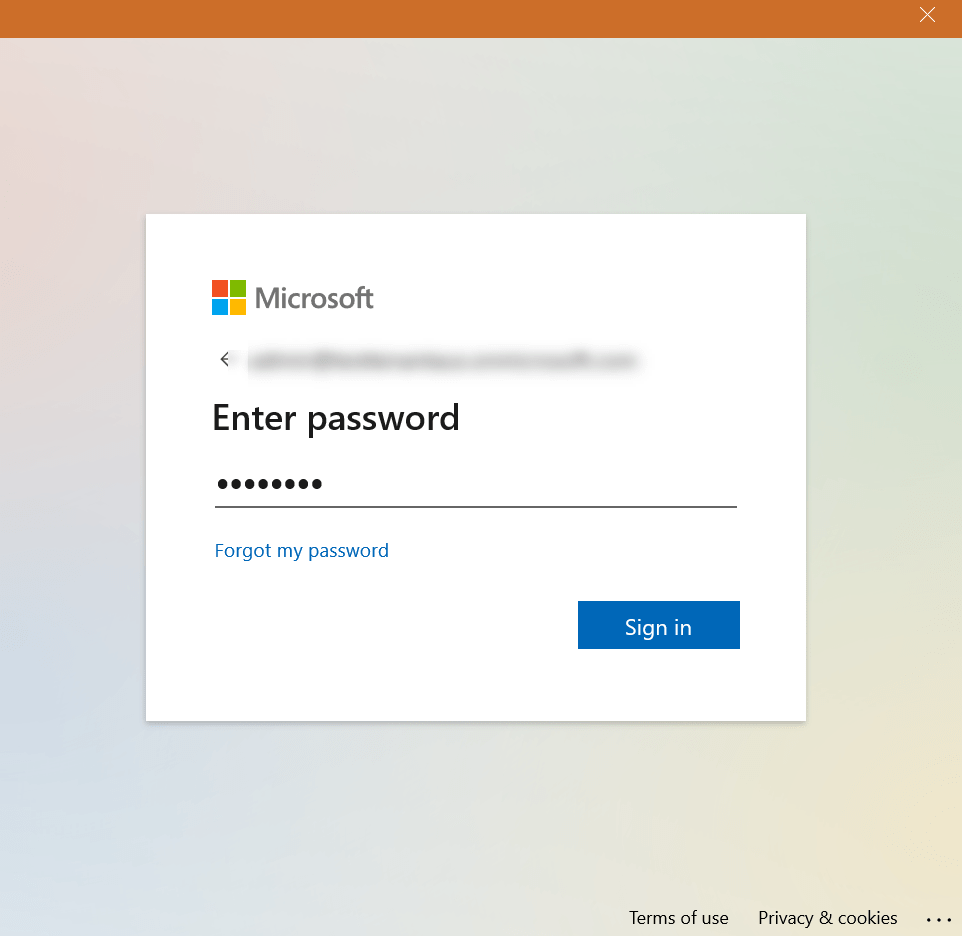
Enter the password that was created for the user account in the Azure portal.
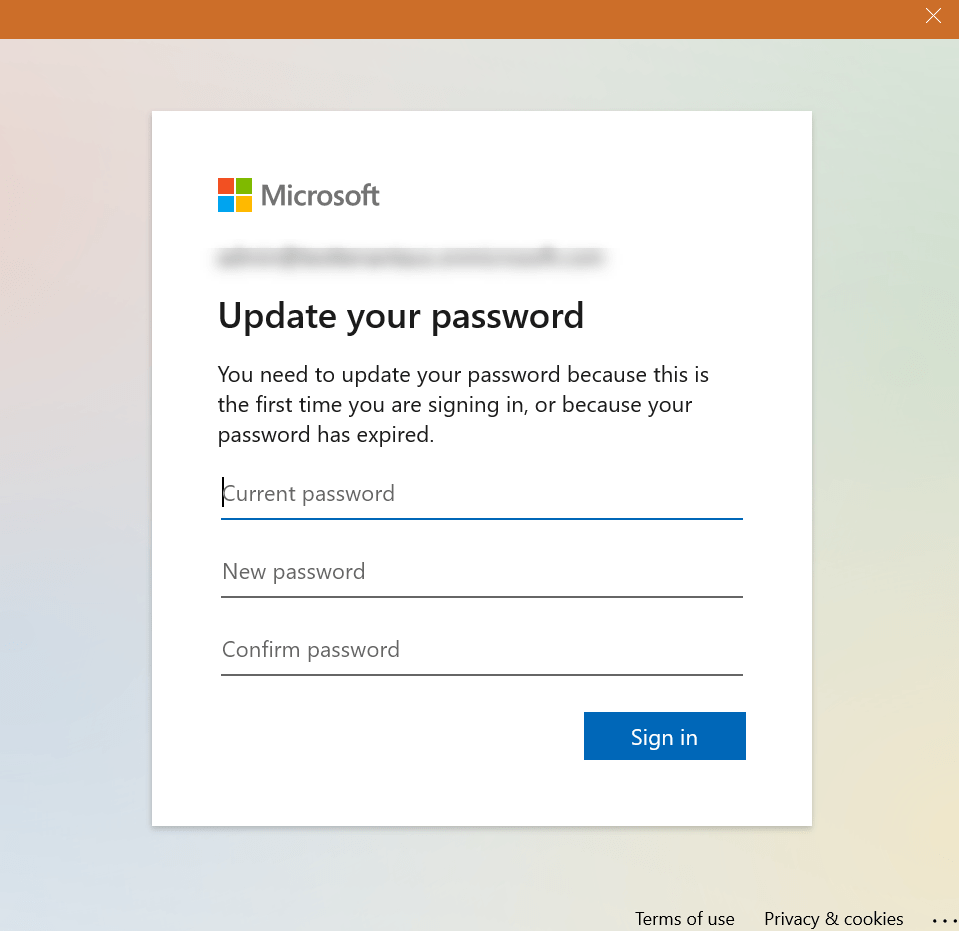
Because we created this account through the Azure Portal, the user password will need to be changed on first sign in.
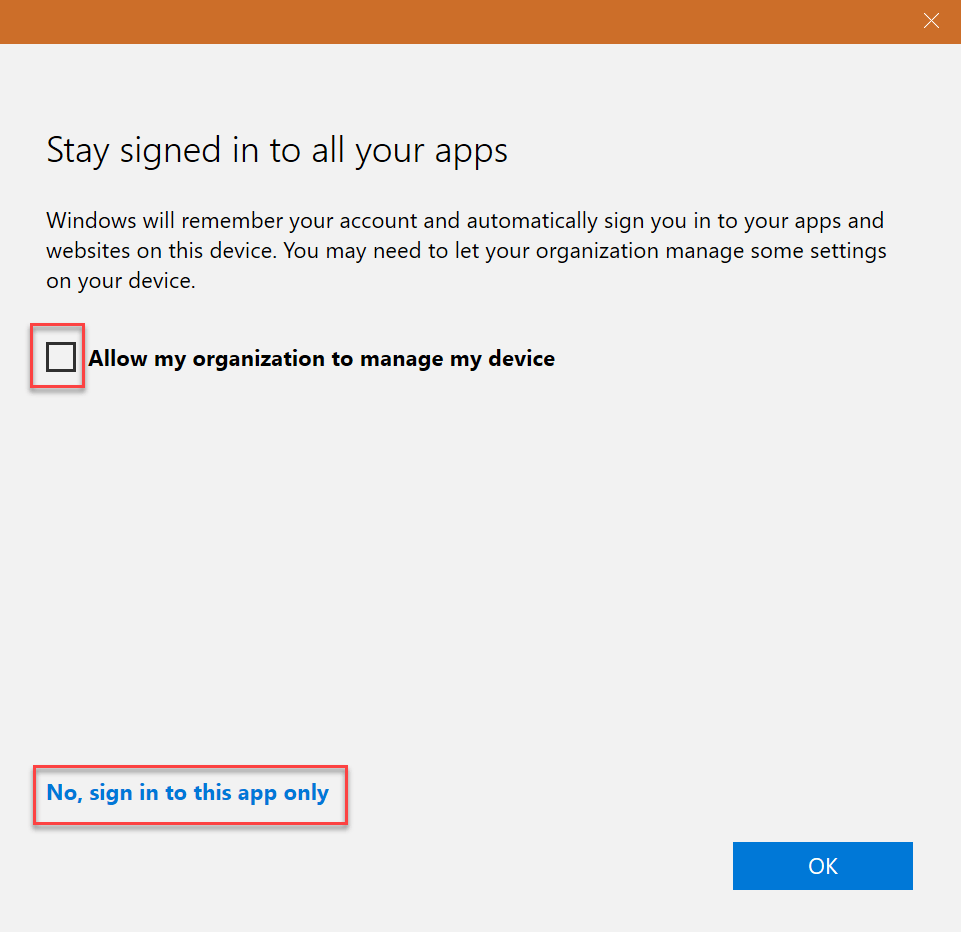
Now this step is important, make sure you deselect Allow my organization to manage my device and then click No, sign in to this app only, unless you are planning on integrating your device with this tenant. In my case, I’m not, the device is managed elsewhere.
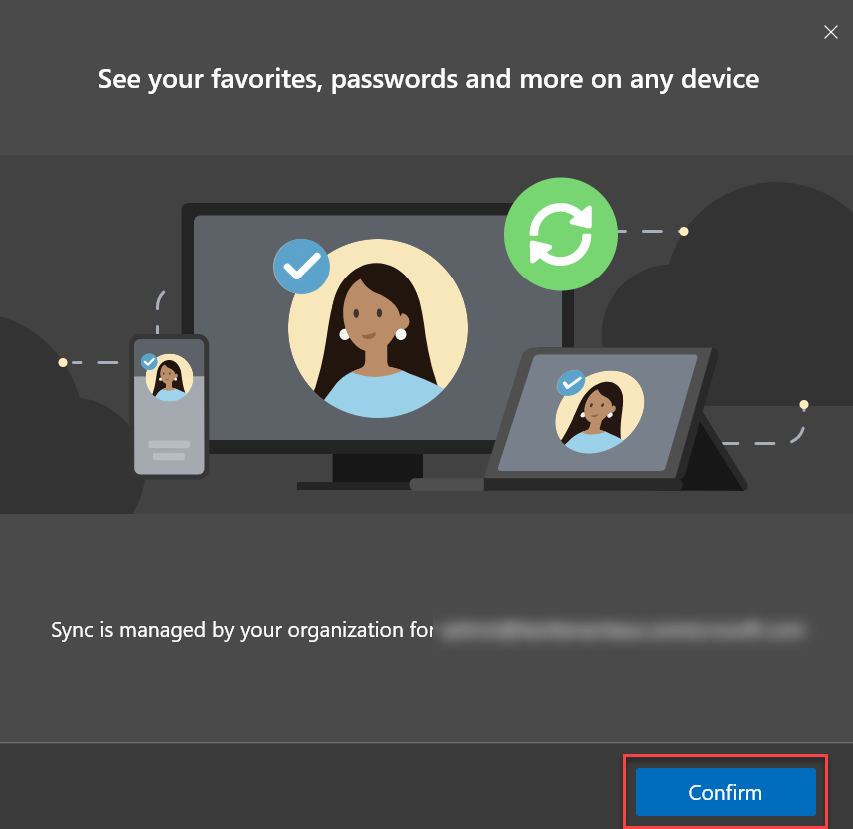
And that brings us to the end of step 2, where we just confirm that we want browser settings to synchronise to other devices.
Step 3: Add the Microsoft 365 Business Premium trial
Sign in to admin.microsoft.com with the new credentials, and go straight to Billing and then Purchase services. Find Microsoft 365 Business Premium, hover over it and choose Start free trial. Make sure you do this first because you lose access to this version of the page with free trials, so don’t be tempted to explore too much just yet or change any settings. I’m not sure if the functionality I’m about to demonstrate will change soon or not, so I’ll provide some other options further down just in case this stops being the initial Purchase services page.
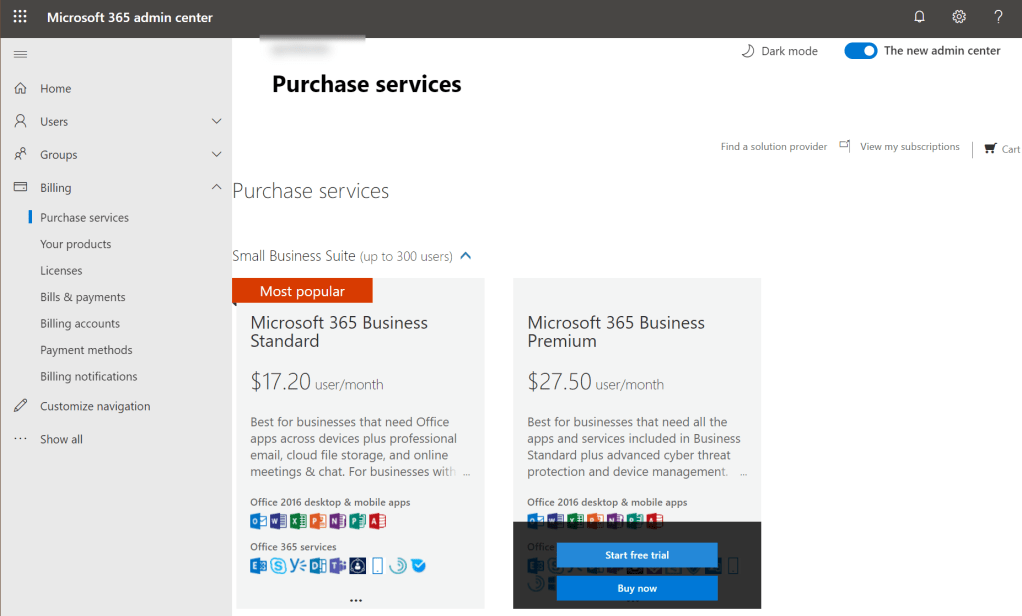
Now, what did I mean about the page changing? Let’s take a look, I’ll switch from Light mode to Dark mode.
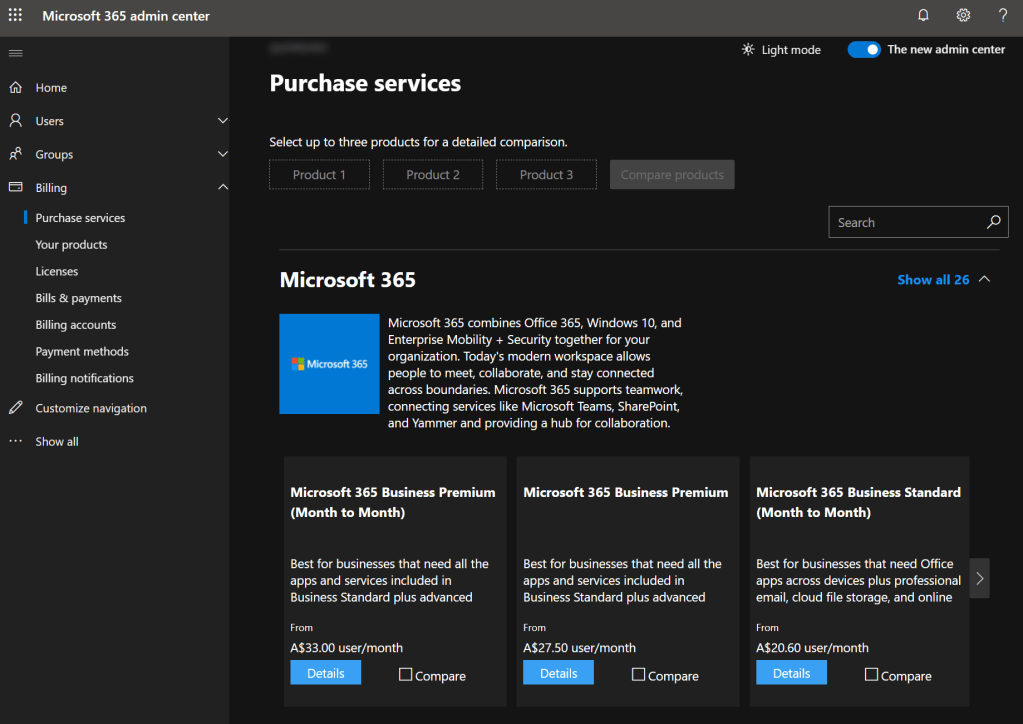
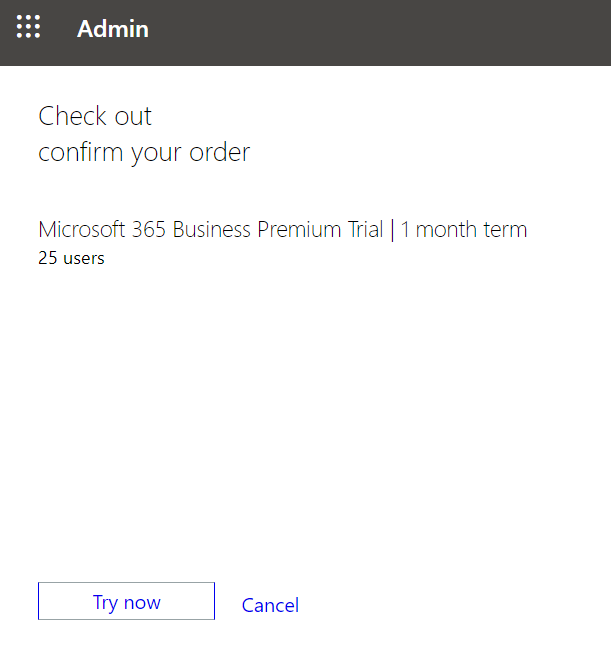
What you should notice here is that it’s a completely different page, and this new page doesn’t include trial links, and neither do the pages this page links to. At this point in time you can still trigger a Microsoft 365 Business Premium free trial by going to this link, but again, I’m not sure how long this option will remain available. You will need to do SMS or phone call based verification to accept the trial, and then you can confirm the trial.
To finish off this post, let’s switch back to Billing, but now go to Your products to ensure that the trial has been added.
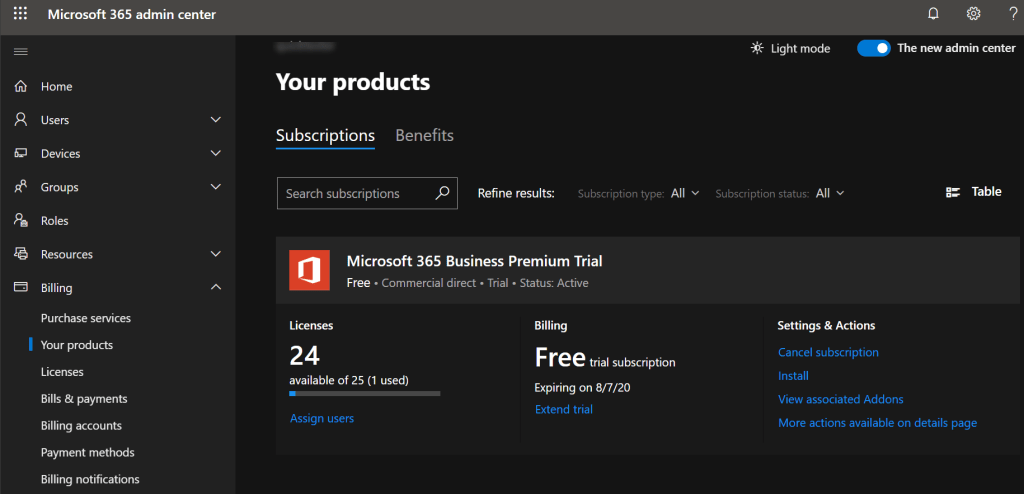
So, this might seem like a long winded way of provisioning a trial subscription, but right now it seems like the most consistent way of being able to get one set up without needing to remember to cancel the trial before you start getting charged. Something that I probably should have mentioned earlier, but I’ll mention it now. I deliberately didn’t choose a Microsoft 365 Enterprise E5 trial, because I wanted to make sure we weren’t working in a Microsoft 365 tenant that wasn’t really a Microsoft 365 Business Premium tenant.
In the next post I’ll cover how we can indirectly add Microsoft Defender Advanced Threat Protection into this environment, without having to resort to something like a Microsoft 365 Enterprise E5 trial. The trial options available don’t include Windows 10 Enterprise E5 or standalone Microsoft Defender Advanced Threat Protection, but there’s another way to bring it in. Stay tuned for details…
Mark, whilst MS announced the MDATP standalone SKU in March 2020, our CSP Provider (Rhipe) seem to be in the dark about it.
Has MDATP standalone reached general availability in Australia?
LikeLike
HI David – yep, it’s available, it’s even on their pricelist – part # E2DCAB13-1365-417A-B624-4901E2B252F5 from what I can see.
LikeLike